Blog Categories
Popular articles
- Installing, configuring, and using OpenVPN server Centos 6.6
- Module Installation php libssh2 on CentOS 6.x
- Mirror CentALT repository for CentOS 5.x - 6.x
- Attention! Critical vulnerability in all versions of Joomla 1.5, 2.5,3 (CVE-2015-8562)
- S.M.A.R.T - monitor the status of hard drives in Centos sending notifications to Email
Basket of services
Company news
- Thursday, 24 December 2015: Merry Christmas and Happy New Year!
- Monday, 20 April 2015: Accepting payments through payment system Webmoney and Z-Payment restored
- Saturday, 18 April 2015: Unavailable accepting payments via Webmoney and Z-Payment
- Thursday, 05 March 2015: To order new services are available - DNS hosting and secondary DNS server
- Wednesday, 25 February 2015: Added new ways to pay for services
Recent blog posts
-
Attention! Critical vulnerability in all versions of Joomla 1.5, 2.5,3 (CVE-2015-8562)
-
Mirror CentALT repository for CentOS 5.x - 6.x
-
Mozilla after Google announced its intention to abandon the valuable work with sites that do not use https
-
Critical vulnerability in Magento
-
Warning! XSS vulnerability in WordPress and a set plug-ins.
Today, faced with the problem of installing php module libssh2 on a server with Centos 6.6 and PHP 5.4.37.
A simple way, like team pecl install ssh2, the module becomes refused flies error "Failed to download pecl/ssh2 within preferred state "stable", latest release is version 0.12, stability "beta", use "channel://pecl.php.net/ssh2-0.12" to install install failed".
To deal with this, I did not, and went the other way.
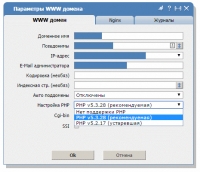
Installation of two versions of php (5.2 and 5.3) on a server with Centos and panel ISPmanager
Thursday, 22 January 2015 00:40PHP version 5.2, though, and already seems to have outlived its function, but still more is needed. After all, there are more old sites that will not work on newer versions of php. For example those that are encoded by Zend 5.2, and they are not alone.
We have: server OS Centos on board, ISPmanager control panel and set the standard method php 5.3.x.
Task: installed on the server and more php 5.2, and implement convenient switching between versions for each site.
The basic version of php we will be the 5.3, as can be updated without any problems, etc., but more will be version 5.2, since its development is completed.
Detected a critical vulnerability in Drupal 7 (SA-CORE-2014-005)
Saturday, 18 October 2014 00:44The company Sektion Eins was found a critical vulnerability, which affects all versions of Drupal 7 branch. It allows you to execute arbitrary SQL-query the database Drupal without any rights in the system. Thus, for example, it is possible with absolutely no rights on your website, create a special request, which will create a new administrator or change the current password. The danger is defined as the highest. October 15 came kernel upgrade to version 7.32, which addresses the vulnerability. Developers are strongly advised to update the kernel immediately.
At the moment, already compromised a lot of sites for this CMS and break-ins continue.
Serious vulnerability in TimThumb. Attention site owners on wordpress!
Monday, 30 June 2014 01:15June 24, 2014 was know about another critical vulnerability in the script timthumb.php, which is used in a huge number of themes and plugins popular engine wordpress. We would like to note that this script is used not only in wordpress, but also in many other CMS, as well as their extensions.
Vulnerability affects all versions of absolutely timthumb, including 2.8.13, as well as the original project WordThumb. The vulnerability allows attackers to run malicious code execution without having access to your site.
Just yesterday, was made public a critical vulnerability in OpenSSL.
The vulnerability is related to the lack of adequate bounds checking in one of the procedures expansion Heartbeat (RFC6520) protocol TLS / DTLS. Due to the small mistakes anyone can gain access to the computer's memory, whose communication "protected" vulnerable version of OpenSSL. In particular, the attacker gains access to the private key, user name and password and all content to be transmitted in encrypted form. When this leaves no traces of penetration into the system.